Customer Success Stories
Read more about how we helped customers like you secure their environment and improve ROI from their investment:
- Finance
A leading UK based wealth management platform provider partnered with FullProxy to bring control and visibility to its highly complex, high-risk encrypted environment. Leveraging F5 technologies, FullProxy enhanced encrypted traffic visibility and control, strengthening security posture while ensuring resilience against evolving threats in a tightly regulated landscape.
- Energy
C&C Group is a leading software manufacturer specialising in designing, developing, delivering, and hosting cloud-based software solutions. Their solutions are primarily used by UK critical infrastructure companies operating in the electricity, water, gas, and healthcare sectors. As a long-standing customer of FullProxy, C&C Group needed to carry out a vital F5 hardware refresh and Bourne series to rSeries migration in order to modernise their network infrastructure and ensure compliance within a regulatory framework.
- Government Relations Services
The Improvement Service team was using terminal-based vulnerability assessment tools, but they needed a more intuitive, user-friendly solution that could provide clear visualisation of security data while meeting the stringent security requirements of public service applications. They were looking for a tool that would streamline their vulnerability management process without sacrificing robust security analysis capabilities.
- Automotive
A car retailer that prides itself on offering the best deals on used cars both online, and in-store, and provides its customers with a wide range of services such as MOTs, selling services, and car hire. During their cyber security journey, they approached FullProxy wanting to maximize ROI for their existing F5 hardware infrastructure, improve application availability and redundancy, whilst protecting critical web services and customer data from increasing levels of cyber-attacks such as, Ransomware and Phishing attempts.
- Local Government
FullProxy’s consultants helped identify which cyber solutions were right for their environment and played a key role in project delivery and operational support, which helped the local community, employees, student population and service partnerships gain secure access to the web application services and data they needed. Having successfully used F5 products for ten years or more it was important for the local authority to continue to maximise return on investment and maintain the lifecycle and security of their application services with minimal impact on their operations, whilst agilely delivering new digital services.
- Higher Education
In today's cyber security landscape, universities face the dilemma of providing seamless yet secure remote access to their staff and students, irrespective of their geographical locations. For a prestigious UK top 20 university with a sprawling network encompassing thousands of individuals dispersed across the UK and beyond, this challenge was particularly daunting.
Application Pen Testing with Improvement Service
The Improvement Service team was using terminal-based vulnerability assessment tools, but they needed a more intuitive, user-friendly solution that could provide clear visualisation of security data while meeting the stringent...

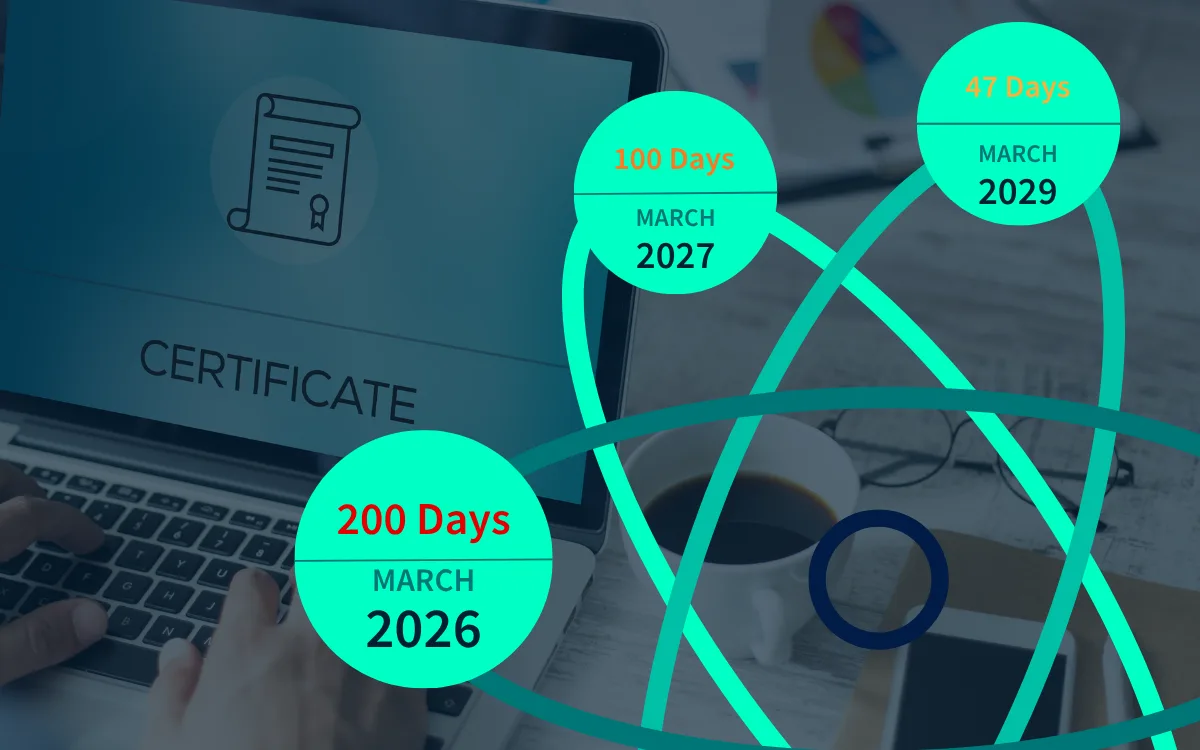
Automating Certificate Management for South East Coast Ambulance Service
By partnering with FullProxy and implementing AppViewX, SECAmb successfully automated their certificate management, reducing workload, improving efficiency, lessening the risk of private patient data being exposed as it is transferred...

F5 Hardware Refresh, Software Upgrade and Configuration Migration with C&C Group
C&C Group is a leading software manufacturer specialising in designing, developing, delivering, and hosting cloud-based software solutions. Their solutions are primarily used by UK critical infrastructure companies operating in the...

F5 optimisation consultancy for Scottish Healthcare Trust
NHS Lothian had discovered their F5 appliances were sailing with improper configurations, leaving their network vulnerable to malicious intruders. With the spectre of cyber threats looming large, including the ominous...

Secure Remote access for Top 20 university using F5 solutions
In today's cyber security landscape, universities face the dilemma of providing seamless yet secure remote access to their staff and students, irrespective of their geographical locations. For a prestigious UK...

Reviewing and Implementing Firewalls for a Games Company
A prominent gaming company approached FullProxy seeking expertise in reviewing and implementing firewalls to strengthen their cybersecurity infrastructure. As a rapidly growing outfit in the games sector, they manage substantial...